Latest draft of the No Stalking for Advertising Term V.2
UX and INTERFACE
Revised DRAFT of a singular, comprehensive term:
PREAMBLE: The User submitted term shown here creates an opportunity for individuals to share their single term with entities about how they wish to be treated. This effort is meant to describe human, legal and machine readable versions of a comprehensive term along with additional information for agents who might implement this term for individuals as well as for entities who might see, accept or refuse the term. {{ Information is defined as personal information provided by the individual about themselves. Data + Meaning = Information. The observer creates meaning (or observer is “informed by” the data), and then can be assigned duties. Information not collected from a person does not by definition constitute personal data. }}
TERMS AGREEMENT: {{ Information can only be shared with those parties who first agree to abide by these terms. Any sharing of information with a party that has not first agreed to these terms is a violation of these terms. }}
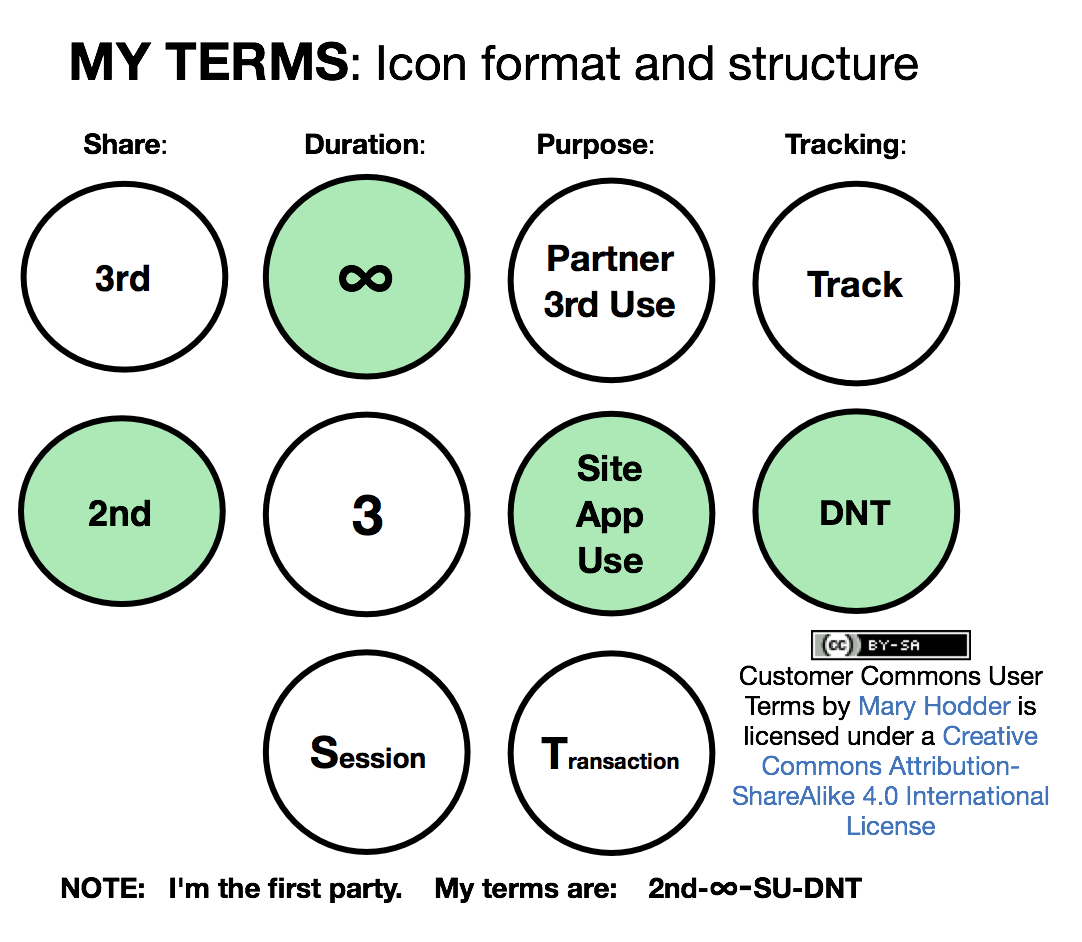
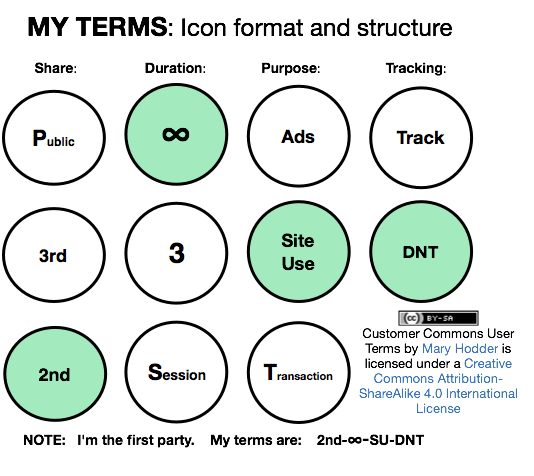
SHARE: describes the terms for sharing information with entities by individuals.
Choice: 2nd
1st-2nd Party: My information shared and what I do will be kept between me and the entity.
{{Information shared by an individual (the “1st party”) and their activities are not permitted to be shared by the 2nd party with any other parties.}}
DURATION: describes the terms for retaining information by entities about individuals. {{ Add language referring to laws or contracts, defining 3rd party jurisdiction, to limit this from abuse. }}
QUESTION: should this be just for the session? or for as long as the person still has a relationship and agrees to sharing?
Choice: Session
Session: My information shared or about what I do will only be kept for the session, unless required by law or contractual obligation.
{{ Information about an individual must be destroyed by the 2nd party immediately after the completion of the transaction for which it was collected or otherwise generated, unless otherwise required by law or contract obligation. }} [NOTE: What about records for audit? What about hashed storage, e.g., in blockchain or other ledger system?]
OR ?
Choice: Infinity
Unlimited until further notice: My information will be kept as long as I continue to choose this term, unless required by law or contractual obligation. If I change to another lesser term, my new term will be followed.
{{ Information about an individual can be retained indefinitely by the 2nd party, unless and until the 1st party notifies the 2nd party they have made an alternate selection for duration. }}
PURPOSE: describes the purpose for use of individual’s information provided or about actions they take
Choice: Site / App Use
Site and App Use: My information will be used for providing and / or enhancing the site or service, but not other purposes without my permission.
{{ Information about an individual may be used beyond the transaction for which it was collected or generated, but only with respect to the operation [or further development?] of the site or app over which such original transaction occurred and not for any other secondary uses by the 2nd party or other parties. }}
TRACKING
Choice: Tracking
Tracking: I will allow myself to be tracked by 3rd parties.
{{ Tracking of individual and their activities by any 3rd parties is authorized. }}