Ordinary people wearing and enjoying the world’s original privacy technology: clothing and shelter. (I’m the one on top. Still had hair then.)
Start here: clothing and shelter are privacy technologies. We use them to create secluded spaces for ourselves. Spaces we control.
Our ancestors have been wearing clothing for at least 170,000 years and building shelters for at least half a million years. So we’ve had some time to work out what privacy means. Yes, it differs among cultures and settings, but on the whole it is well understood and not very controversial.
On the Internet we’ve had about 21 years*. That’s not enough time to catch up with the physical world, but hey: it’s still early.
It helps to remember that nature in the physical world doesn’t come with privacy. We have to make our own. Same goes for the networked world. And, since most of us don’t yet have clothing and shelter in the networked world, we’re naked there.
So, since others exploit our exposure — and we don’t like it — privacy on the Internet is very controversial. Evidence: searching for “privacy” brings up 4,670,000,000 results. Most of the top results are for groups active in the privacy cause, and for well-linked writings on the topic. But most of the billions of results below that are privacy policies uttered in print by lawyers for companies and published because that’s pro forma.
Most of those companies reserve the right to change their policies whenever they wish, by the way, meaning they’re meaningless.
For real privacy, we can’t depend on anybody else’s policies, public or private. We can’t wait for Privacy as a Service. We can’t wait for our abusers to get the clues and start respecting personal spaces we’ve hardly begun to mark out (even though they ought to be obvious). And we can’t wait for the world’s regulators to start smacking our abusers around (which, while satisfying, won’t solve the problem).
We need to work with the knitters and builders already on the case in the networked world, and recruit more to help out. Their job is to make privacy policies technologies we wear, we inhabit, we choose, and we use to signal what’s okay and not okay to others.
The EFF has been all over this for years. So have many developers on the VRM list. (Those are ones I pay the most attention to. Weigh in with others and I’ll add them here.)
The most widely used personal privacy technology today is ad and tracking blocking. More than 200 million of us now employ those on our browsers. The tools are many and different, but basically they all block ads and/or tracking at our digital doorstep. In sum this amounts to the largest boycott in human history.
But there’s still no house behind the doorstep, and we’re still standing there naked, even if we’ve kept others from planting tracking beacons on us.
One of the forms privacy takes in the physical world is the mutual understanding we call manners, which are agreements about how to respect each others’ intentions.
Here at Customer Commons, we’ve been working on terms we can assert, to signal those intentions. Here’s a working draft of what they look like now:
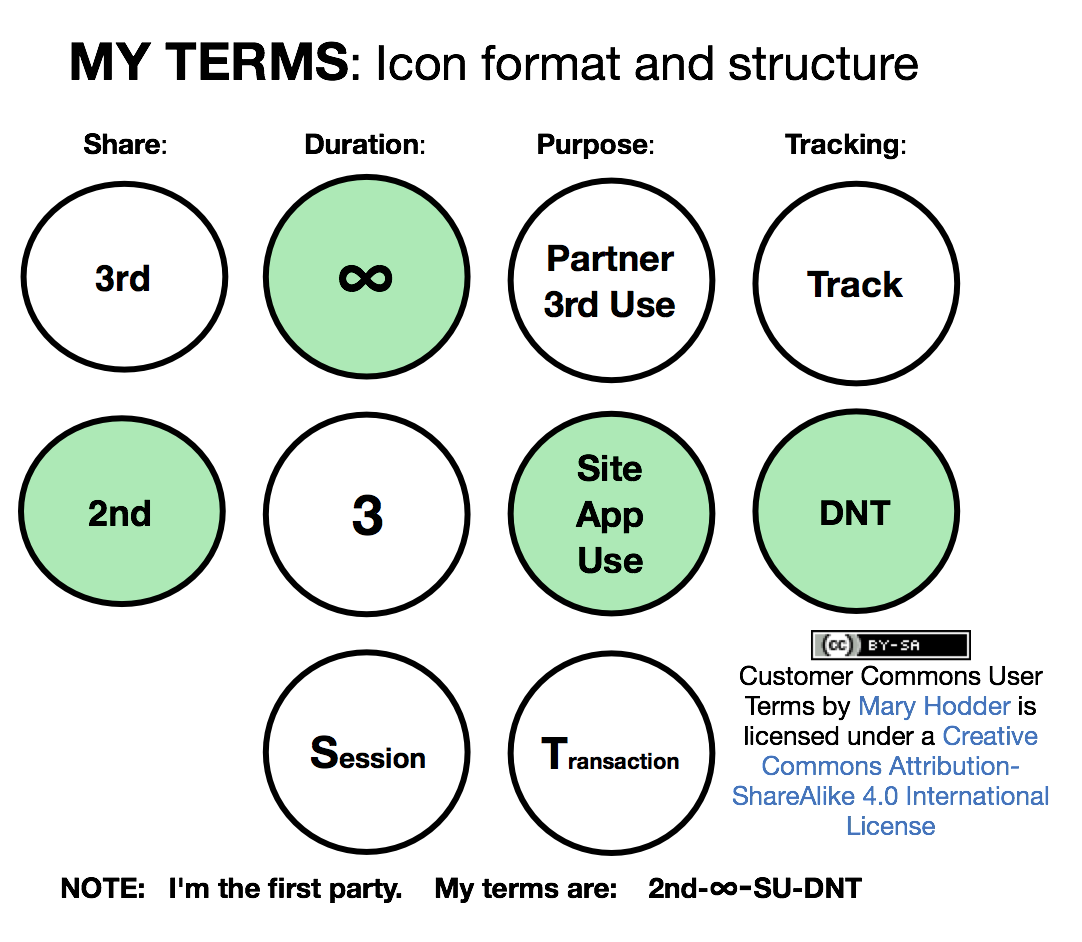
That’s at the Consent and Information Working Group. Another allied effort is Consent Receipt.
If you’re working on privacy in any way — whether you’re a geek hacking code, a policy maker, an academic, a marketer trying to do the right thing, or a journalist working the privacy beat — remember this: Privacy is personal first. Before anything else. If you’re not working on getting people clothing and shelter of their own, you’re not helping where it’s needed.
It’s time to civilize the Net. And that’s an inside job.
__________________
*If we start from the dawn of ISPs, graphical browsers, email and the first commercial activity, which began after the NSFnet went down on 30 April 1995.