Authors: Mary Hodder and Elizabeth Churchill
Creative Commons licenced: by-nc-nd 
©Customer Commons, 2013
Contact: Mary Hodder, [email protected]
Abstract
A large percentage of individuals employ artful dodges to avoid giving out requested personal information online when they believe at least some of that information is not required. These dodges include hiding personal details, intentionally submitting incorrect data, clicking away from sites or refusing to install phone applications. This suggests most people do not want to reveal more than they have to when all they want is to download apps, watch videos, shop or participate in social networking.
Keywords: privacy, personal data, control, invasion, convergence
Download a PDF of the paper here.
Survey
Customer Commons’ purpose in conducting this research is to understand more fully the ways in which people manage their online identities and personal information. This survey, the first of a planned series of research efforts, explores self-reported behavior around disclosure of personal information to sites and services requesting that information online. We believe the results of this survey offer a useful starting point for a deeper conversation about the behaviors and concerns of individuals seeking to protect their privacy. Subsequent research will explore how people feel and behave toward online tracking.
This research is also intended to inform the development of software tools that give individuals ways to monitor and control the flow and use of personal data.
For this research project, Customer Commons in late 2012 surveyed a randomized group of 1,704 individuals within the United States (1,689 finished the survey, or 95%). Respondents were geographically distributed, aged 18 and up (see the appendix for specifics), and obtained through SurveyMonkey.com. The margin of error was 2.5%.
Respondents gave checkbox answers to questions and in some cases added remarks in a text box. (Survey questions and answers are in an addendum to this paper.)
Key Findings
Protecting personal data
This survey focused on the methods people use to restrict disclosure of requested personal information. Those methods include withholding, obscuring or falsifying the requested information.
Only 8.45% of respondents reported that they always accurately disclose personal information that is requested of them. The remaining 91.55% reported that they are less than fully disclosing. If they decide the site doesn’t need personal information such as names, birthdates, phone numbers, or zip codes, they leave blank answers, submit intentionally incorrect information, click away from the site, or — in the case of mobile applications, decline to install.
Most people withhold at least some personal data. Specifically,
- 75.7% of respondents avoid giving their mobile numbers
- 74.8% avoid “social” login shortcuts such as those provided by Facebook or Twitter
- 73.4% avoided giving sites or services access to a friend or contact list.
- 58.3% don’t provide a primary email address
- 49.3% don’t provide a real identity
The concept of trust was raised in 22% of the written responses explaining why people hide their information. Some examples include:
- “I cannot trust a random website”
- “I do not want spam and do not want to expose others to spam. I also don’t know how that information could be used or if the people running the site are trustworthy.”
- “If I know why info is needed then I might provide, otherwise no way”
- “I felt the need to cover my I.D. a little bit — like age and gender. And I still withhold my social security #.”
- “If I feel they don’t need it to provide a service to me they don’t get it even if I have to enter in fake info”
- “Worries on identity theft and general privacy.”
- “i would never give out my friends or and familys (sic) info ever”
Many respondents said sites and services request more data than required. Others suggested that providing requested information would result in an increased risk to their security. More results:
- When the 71% of respondents who reported withholding information were asked why, they said they didn’t believe the sites needed the information. Specifically,
- 68% reported they either didn’t know the site well when they withheld their data or didn’t trust the site.
- 45% of those who felt they knew the site or service well still withheld information.
Respondents lied about various line items as a strategy to protect their privacy. For example, 34.2% intentionally provided an incorrect phone number, and 13.8% provided incorrect employment information. Here are some reasons they gave:
- “I didn’t want them to have all my information, or feel it was necessary.”
- “I have obscured various information so that I would not have further contact with a vendor who won’t leave me alone”
- “Faking it is the best to avoid unwanted contact”
- “Sometimes you just want to use a service without them knowing every thing about you.”
- “I don’t like websites to have very much information on me. I regularly give out spam email addresses, bad birthday dates, and bad location information.”
- “Registering for many mundane website often requires some pretty detailed personal info. I generally fudge this. None of their business”
- “Because information is so easily found and transferred on the internet I do provide false info quite often to protect my identity.”
Even those who had never submitted incorrect information made statements such as:
- “Have never made up info – just ignored requests :-)”
- “i just don’t use that website”
- “I have an email address that is purly (sic) for junk mail. I use this email address for websites that request my email address and then I go into that email and delete all email monthly.”
- “I have never given incorrect information, but I have thought about it.”
- “I don’t lie, but I omit as I feel appropriate.”
Going with the flow
Correcting already obscured or falsified information appears to be too much of a chore. Specifically,
- Over 50% have rarely or never corrected data they submitted incorrectly
- 30% correct their data “sometimes.” Of that 30%,
- 55% said a purchase required correct information
- 56% had a growing feeling of comfort with the site or service
- 46% cited the ability to realize new benefits from the site with corrected information
- 30% said they noticed others’ incorrect data at Facebook or other social sites, or in phone applications, and —
- 80% of this group assumed that the data was falsified as a way to protect privacy
- 40% believed the incorrect data was there to mislead marketers
- 12% believed secretive associates were trying to mislead them
- 13% believed services always needed correct personal information
- 75% believed the services needed it only sometimes
- 12% said it was never needed.
Respondents also believed that other users of these services always needed or expected correct personal data about each other 27% of the time, whereas 23% said it was sometimes needed, and 48% said it was never needed.
Privacy online
The results of this survey support the hypothesis that people limit, refuse to give or obfuscate personal information in an attempt to create a measure of privacy online.
On July 30, 2010, in the first article in its “What They Know” series, The Wall Street Journal reported, “One of the fastest-growing businesses on the Internet … is the business of spying on Internet users. The Journal conducted a comprehensive study that assesses and analyzes the broad array of cookies and other surveillance technology that companies are deploying on Internet users. It reveals that the tracking of consumers has grown both far more pervasive and far more intrusive than is realized by all but a handful of people in the vanguard of the industry.”[i]
Adds Doc Searls, in The Intention Economy, “Tracking and ‘personalizing’—the current frontier of online advertising—probe the limits of tolerance. While harvesting mountains of data about individuals and signaling nothing obvious about their methods, tracking and personalizing together ditch one of the few noble virtues to which advertising at its best aspires: respect for the prospect’s privacy and integrity, which has long included a default assumption of anonymity.”[ii]
This survey showed one result of this system. Respondents expressed a general lack of trust in their relationships with online businesses. Many feelings ran strong. Here are some of the comments:
- “Scary world out there, and I am a bit angry about the fact that all these website ‘track me’ as if that is OK, and then they sell MY data, obviously making money in the process. How is that OK or even legal? Don’t I control MY information? Apparently not…”
- “So if I think it might be ‘harmful’ to give out info, I don’t do it.”
- “I want cookies outlawed 🙁
- “My ex-husband was abusive and has stalked me. I don’t need to let the greedy sellers of my personal information draw him a map to my front door.”
- “While I doubt I have any real protection of privacy, I have a desire to try to send a message that I want my right to protection of privacy. I regret how much we as a society have lost to the powers of marketing.”
- “I don’t trust the security procedures of most companies. Security costs money, which cuts into profits, thus most companies have limited incentive to protect PII from cyber criminals.”
- “The web is far less secure than commonly known.”
- “Just as I have disconnected my land line because of a flood of unwanted calls, I refuse to give online/ access information for the same reason.”
These survey responses show people resort to withholding data or submitting false data to avoid feeling exposed online. When deciding whether to share personal information, the majority of respondents doubt that sites or services need to collect more than a minimum of obviously necessary personal data.
Conclusion
When people withhold personal data, it is to create a sense of privacy and control of their personal lives.
People are afraid or distrustful of sites, services and phone apps that request their personal data. They withhold or falsify information because they do not believe the sites need their data, and because they do not want to disclose information that might lead to spamming or other intrusions. Moreover, the techniques that people employ to preserve their sense of privacy online are largely improvised, informed by fear, and based on their subjective evaluation of entities that solicit personal information.
For the sake of privacy, people contribute to and tolerate the presence of incorrect personal data online, and attempt to correct it only when they see the clear upsides of accuracy. And, despite the failure of businesses and other organizations to convince users of the need to provide personal details beyond an email address, most users remain comfortable disclosing additional personal data only with those they know and trust.
Research Funding Grant
This research project was funded with a grant from CommerceNet, a not-for-profit research institute working to fulfill the potential of the Internet since 1993.
Customer Commons
Customer Commons is a not-for-profit working to restore the balance of power, respect and trust between individuals and the organizations that serve them, especially in the online world. We stand with the individual and therefore do not take contributions from commercial entities.
ADDENDUM: Questions and Answers
Click here to see the complete questions, answers and written answers offered by people to provide additional information.
[i] Julia Anguin, “The Web’s New Gold Mine: Your Secrets” The Wall Street Journal, July 30, 2010. http://online.wsj.com/article/SB10001424052748703940904575395073512989404.html
[ii] Doc Searls, The Intention Economy: When Customers Take Charge. (Cambridge, Massachusetts: Harvard Business Review Press, 2012). P. 28.

 In
In 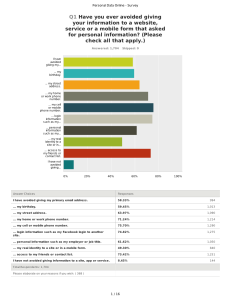




 A lot of big companies are eager to get their hands in your pockets — literally. They want your mobile phone to work as a
A lot of big companies are eager to get their hands in your pockets — literally. They want your mobile phone to work as a 










