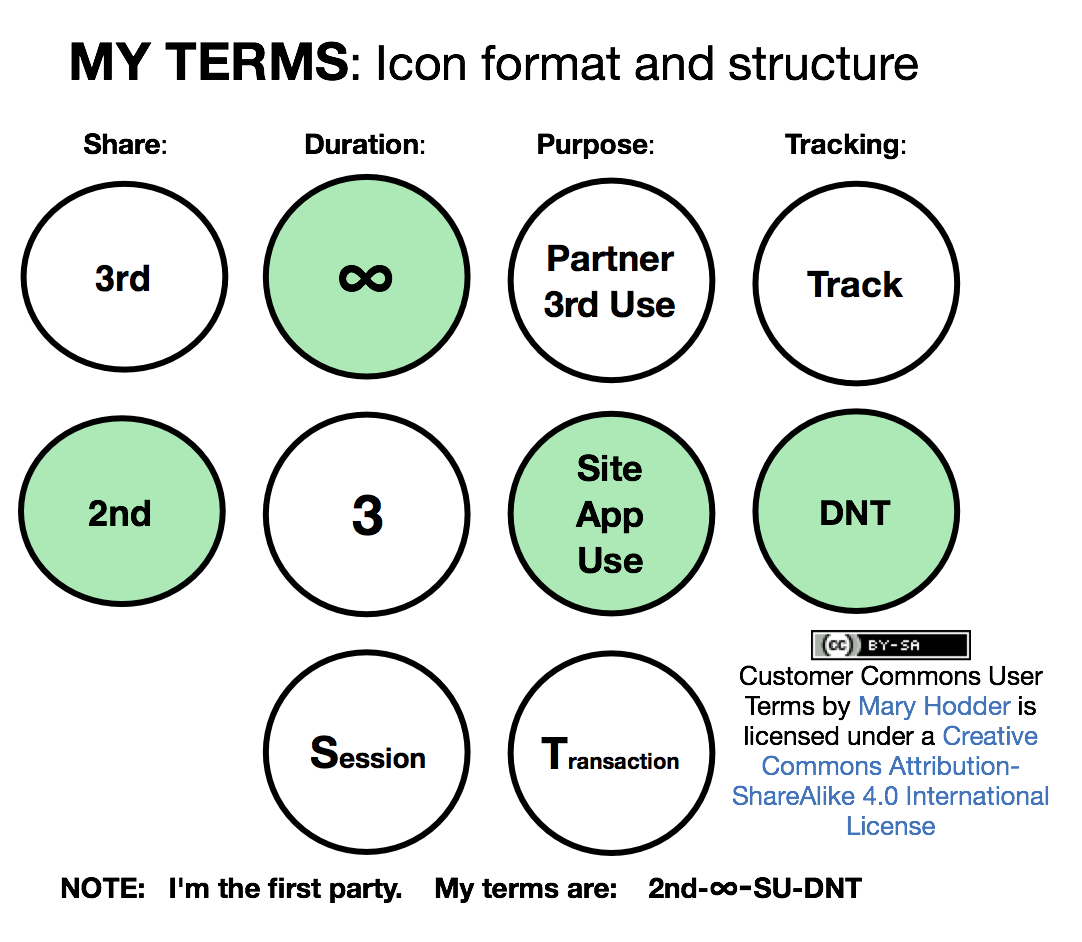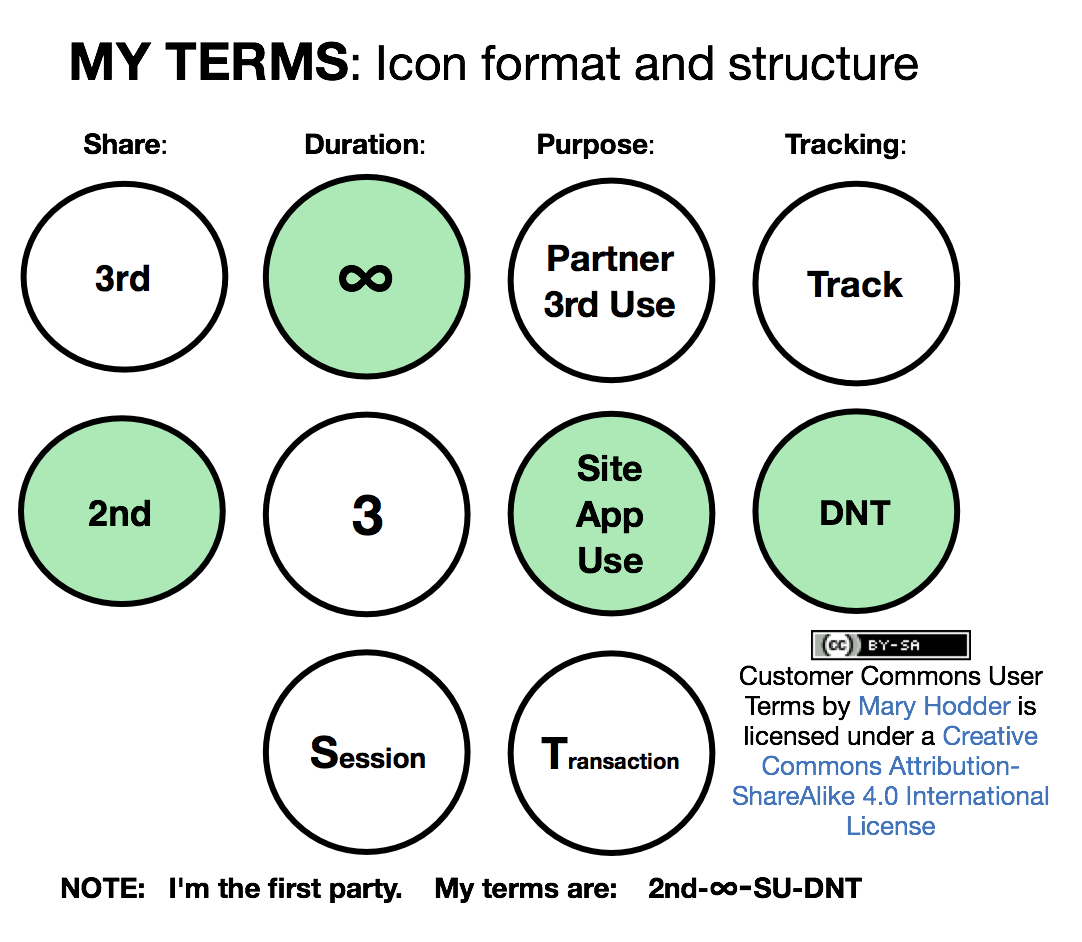
User Terms Draft 2 Icons
Terms are choices you make to ask that your data and activities be treated a certain way. Customer Commons is developing terms with Kantara and the Consent and Information Sharing Working Group so that we have a standardized set of terms, which can commonly be used through browsers, apps and other forms.
It is our intention that Terms will come in Human, Legal and Engineering forms so that people can read them, they can be legally binding, and apis and code will convey and negotiate your chosen terms. The idea isn’t that you would constantly be choosing these things, but rather have your agent take your choices and negotiate for you. We also envision being able to copy someone else’s terms you trust, if you don’t understand what these choices will mean for you.
Terms may also be created that fit with various contexts, like how to handle your health data, or what to do about data you share for a purchase, verses data you share for social activity. Those will come later after the initial set is developed. What you see in the picture above are draft icons. We intend to develop prettier versions with a designer, and work with engineers to develop sample or open source code for both choosing terms, as well as responding to those term requests from individuals.
If you are interested in helping with this project, you can join CISWG UX Kantara, by getting on the mail list, signing the IP agreement (so that all contributions can be used in the project) and getting on our calls. We hope to see you there. Or comment here with questions!